Provide a secure, reliable, and scalable method to remotely access and manage cellular-connected ITS field devices (CMS, CCTV, Controllers, Sensors) without exposing them to the public internet or relying on fragile network configurations.
Secured Cellular ITS
Secure Cellular Connectivity Architecture for Field ITS Devices
Purpose
Background / Problem Statement
ITS field devices deployed over LTE/5G cellular networks operate behind carrier-managed infrastructure that includes firewalls and network address translation (NAT). These controls are intentional and designed for security and scalability, but they introduce challenges such as:
As deployments scale, maintaining consistent, secure access to field devices becomes increasingly difficult.
Cellular Network Constraints (By Design)
Cellular providers commonly enforce:
- Carrier-grade NAT (CGNAT) preventing direct inbound connections to field devices.
- Firewall rules blocking unsolicited inbound traffic.
- Limited native encryption: data is encrypted over the air (only to towers), but traffic inside the carrier core (e.g., GTP transport) is not end-to-end encrypted. Therefore compromising the full end-to-end encryption.
- Dynamic IP addressing, which complicates consistent device reachability.
- Session resets due to mobility or signal variation.
These characteristics make inbound-initiated connectivity unreliable or infeasible in many field environments.
Proposed Connectivity Model
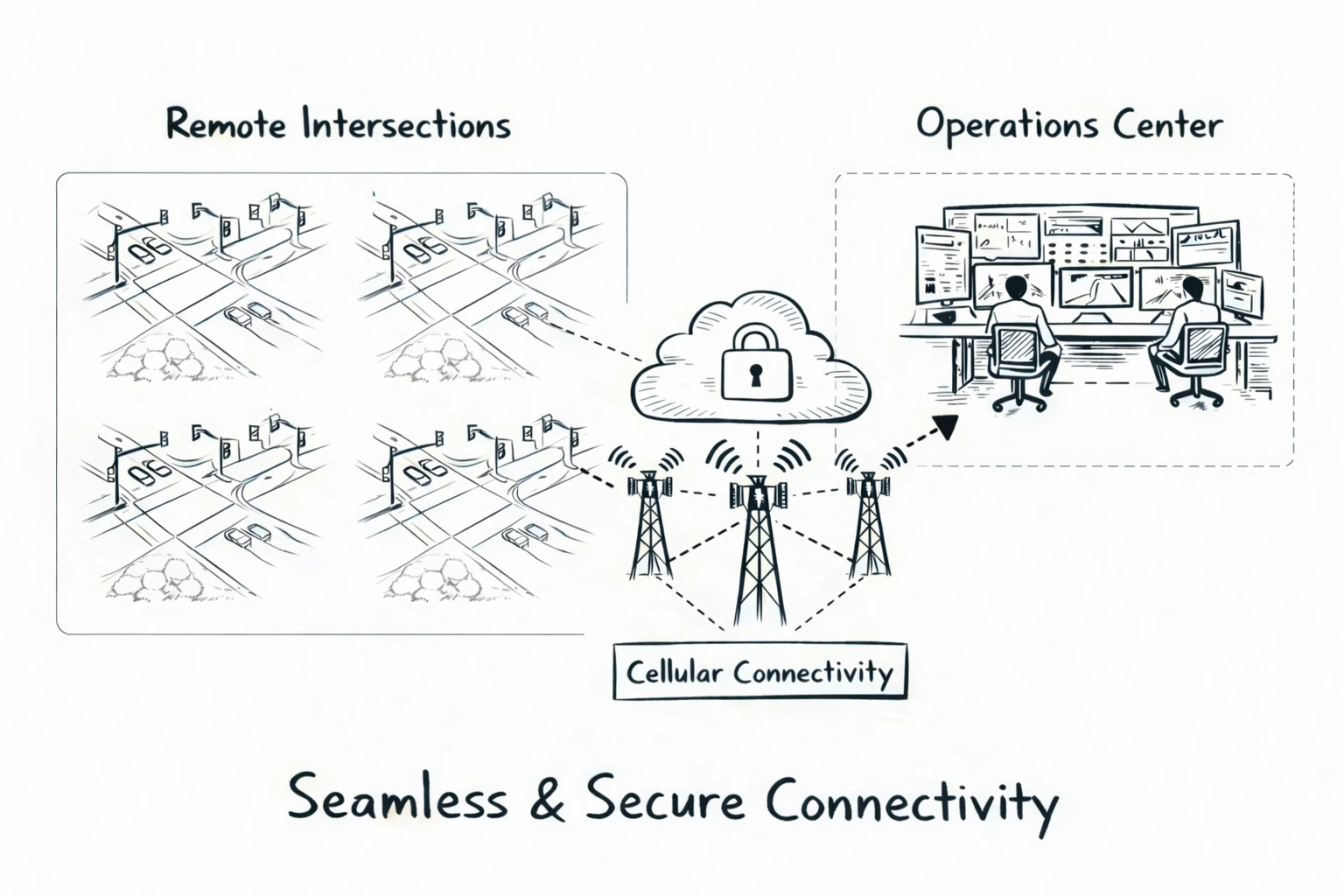
Once established:
- Devices communicate using encrypted peer-to-peer paths
- When direct paths are restricted, traffic automatically transitions to a secure, encrypted failover path
- All traffic remains end-to-end encrypted regardless of transport path.
- Security is further enhanced with two layers of automatic key rotation: one to continuously verify device identity, and another to ensure past data remains protected if a key is ever compromised.
- Zero inbound exposure: No public IPs, ports, or firewall rules required on devices.
- True zero-touch provisioning. Simply power on and connect; L8 automatically handles all setup and management with no customer configuration required.
This zero-trust approach ensures reliable reachability while eliminating traditional attack vectors.
Security & Governance Controls
L8 architecture supports strict ITS security governance through Intelligent Control Layers:
- No public IP addresses assigned to field devicess.
- No inbound firewall rules or port forwarding.
- Strong device identity and mutual authentication.
- End-to-end encryption for all traffic.
Advanced Policy Enforcement
- ITS Focused Network access policies that define which systems, users, and services are authorized to communicate with each device.
- Identity-based, least-privilege access aligned with role-based operations.
- Centralized policy enforcement to ensure consistent security posture across all field locations.
- (Q4 2026) Geo-fencing controls to restrict device network access by approved geographic regions. Location-based connectivity enforcement prevents unauthorized cellular usage by automatically suspending data services when a device operates outside its assigned jurisdiction.
This enables agencies to enforce transportation cybersecurity policies while minimizing human error.
Operational Benefits
- Carrier-agnostic: Compatible with all major LTE/5G providers.
- Resilient: Adapts to IP changes, mobility, and network variability.
- Reduced attack surface: Superior to legacy VPNs by eliminating inbound access.
- Simplified deployment: Minimal field configuration; scales from tens to thousands of devices.
- Low operational overhead: Reduced maintenance and troubleshooting.
Applications
This architecture is well-suited for public-sector ITS deployments where:
- Devices span wide geographic areas and multi-jurisdictional footprints, with aging or unreliable fixed infrastructure (e.g., degraded/ damaged copper lines).
- Inter-agency interoperability is a requirement for cities to securely interconnect TMCs.
- Cellular is used as a primary or resilient backup transport.
- Security, auditability, and policy enforcement are mandatory.
- High uptime and operational simplicity are essential.
Too Long Didn't Read (TL;DR)
Purpose-built for ITS, this outbound-initiated, encrypted connectivity model combines geo-fencing, intelligent access controls, and network awareness to securely manage cellular field devices while reducing risk, simplifying operations, and scaling confidently to meet public-sector cybersecurity demands.
Ready to Connect Your Infrastructure?
Contact us today to discuss your connectivity needs and get a custom quote.