Key Challenges
Devices operating behind carrier-grade NATs and restrictive firewalls make inbound connections unreliable, while public IP addresses increase exposure to cybersecurity risks. At the same time, traditional VPN solutions are often complex to deploy and maintain, introducing security gaps that can undermine true end-to-end encryption, and overall network behavior can vary significantly depending on the carrier and fluctuating signal conditions.
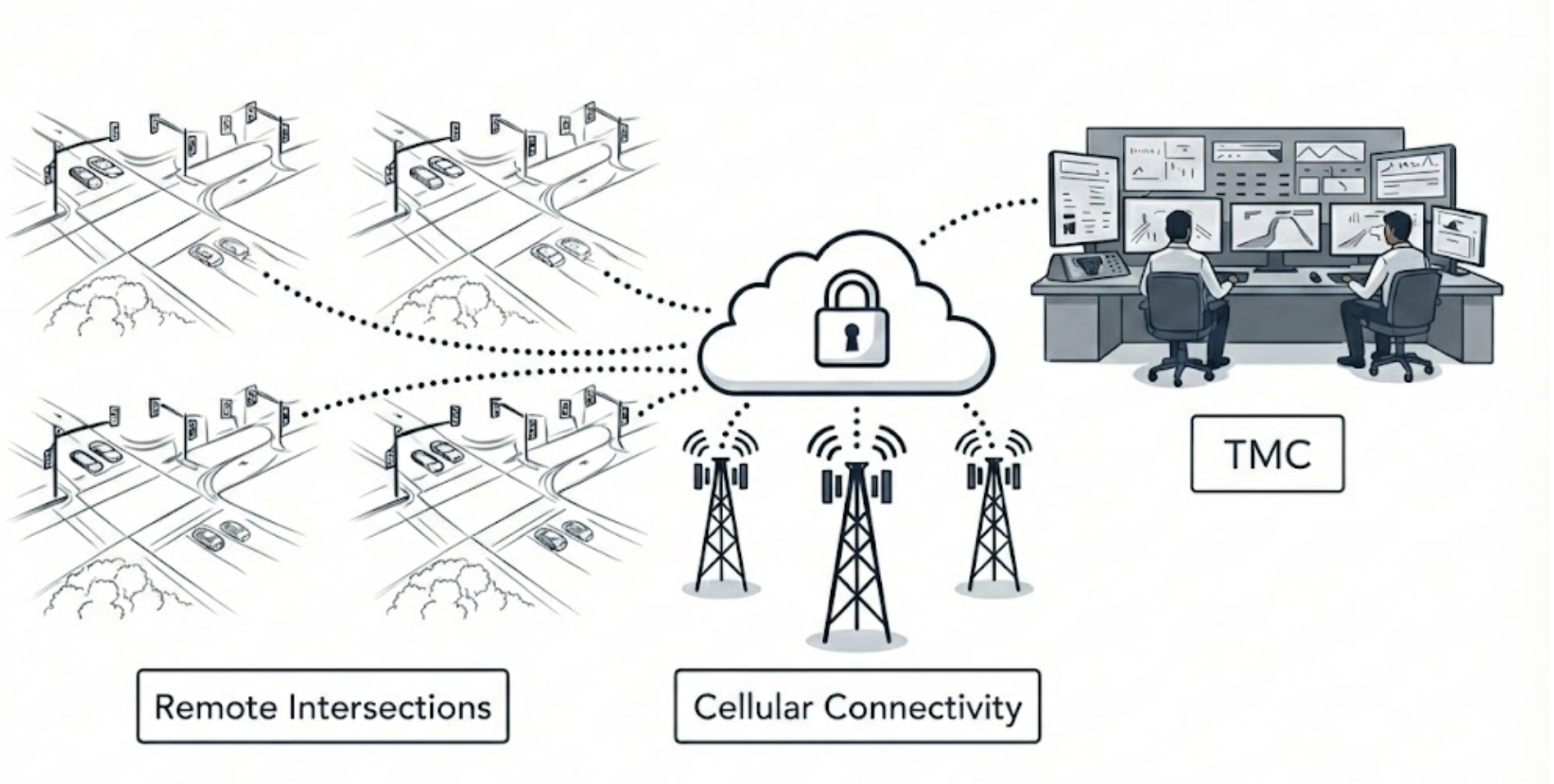
L8 Connectivity Model
- Outbound-initiated – Zero inbound exposure → no public IPs or open ports/port forwarding.
- Peer-to-peer encrypted paths w/ automatic failover when blocked.
- All traffic remains end-to-end encrypted regardless of transport path.
- Two layers of key rotation: Verify device identity continuously. Protect past data if a key is compromised.
- Network access policies that are specially designed for ITS systems, users, and services.
- True zero-touch provisioning. Just power on and connect.
Operational Benefits
- Works across all 5G carriers.
- Reduced cyberattack surface vs. legacy VPNs.
- Simplified deployment and scalable.
- Low-latency performance.
Why L8 Fits Public Agencies
- Ideal for widely distributed devices.
- Cellular as primary or backup transport.
- Strict security and audit controls.
- High uptime.